Red Team Assessment
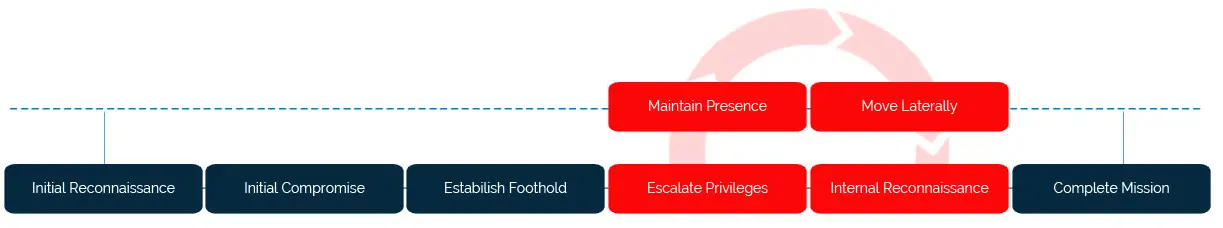
The goal of the Red Team Assessment is to assess the effectiveness of Customer information security prevention, detection, and response capabilities by leveraging real-world adversarial techniques to attempt to penetrate the external perimeter, establish a foothold on the internal environment, and accomplish specific attack objectives mutually defined by Customer and LMNTRIX.
Example objectives may include gaining access to customer data, compromising internal domain administrator credentials, or demonstrating access to email or critical business systems. In order to present a realistic attack scenario, the test will be conducted with no prior knowledge of or access to Customer’s IT environment. Additionally, LMNTRIX will use techniques specifically designed to evade detection by IT Security teams and controls.
- 1
Identification
The goal of this step is to identify, assess, and catalog both human and technical targets that would be most susceptible to compromise by an external adversary.


- 2
Exploitation

Technical Exploitation

Social Engineering
The ultimate goal of Exploitation phase is to breach the perimeter and access internal systems. Technical exploitation is often accomplished by compromising Internet-facing systems and leveraging that access to attack adjacent systems within the environment. Social engineering exploitation is often achieved by obtaining valid credentials that can be leveraged to access the environment via remote access solutions (e.g., VPNs) or via execution of malware on the user’s machine that allows LMNTRIX to operate within the internal environment under the context of the user.
- 3
Post-Exploitation

Privileged Escalation

Internal Exploitation

Credential Harvesting
A secondary objective of this assessment is to measure the detection and response capabilities of the information security team. Therefore, LMNTRIX will use testing and attack techniques that are designed to bypass or evade security controls. LMNTRIX will leverage custom malware that may not be detected by commercial anti-virus products, and avoid using any scanning or exploitation techniques that are likely to be observed by system users or detected by network sensors and endpoint controls. In the event that Customer information security team detects the test in progress, the LMNTRIX and Customer project managers will select an appropriate course of action for the continuation of testing.
Red Team activities will be discussed and agreed upon by both LMNTRIX and the Customer during the project kickoff meeting. This agreement may include the specific scope of the engagement (e.g., whitelisted targets, blacklisted targets), coordination and approval necessary prior to exploitation of targets, schedules and timeframes, data handling and communications plan, and escalation policy.

We help you
- Test your security team’s effectiveness in dealing with a cyber attack
- Train your team to better respond to future cyber attacks
- Determine the level of effort required to compromise your sensitive data or IT infrastructure
- Identify and mitigate complex security vulnerabilities before an attacker exploits them
- Receive fact-based risk analysis and recommendations for improvement
What You will get
- A high-level executive summary of the Red Team Assessment, catering towards executives and senior-level management
- A detailed report describing actions taken during the assessment and a report of all found vulnerabilities
- Fact-based risk analysis detailing the relevance of each vulnerability with respect to your environment, and techniques to validate said vulnerabilities
- Strategic recommendations for long-term improvement

Ready toGet Started?
- CONTACT
- US 888-388-1879
- AU +61.288.805.198
- UK +44.808.164.9442
- SG +65-3129-2639
- IN +91-22-49712788


