LMNTRIX® for IOT/OT
The LMNTRIX architecture and technology stack provides complete support for ICS/SCADA environments.
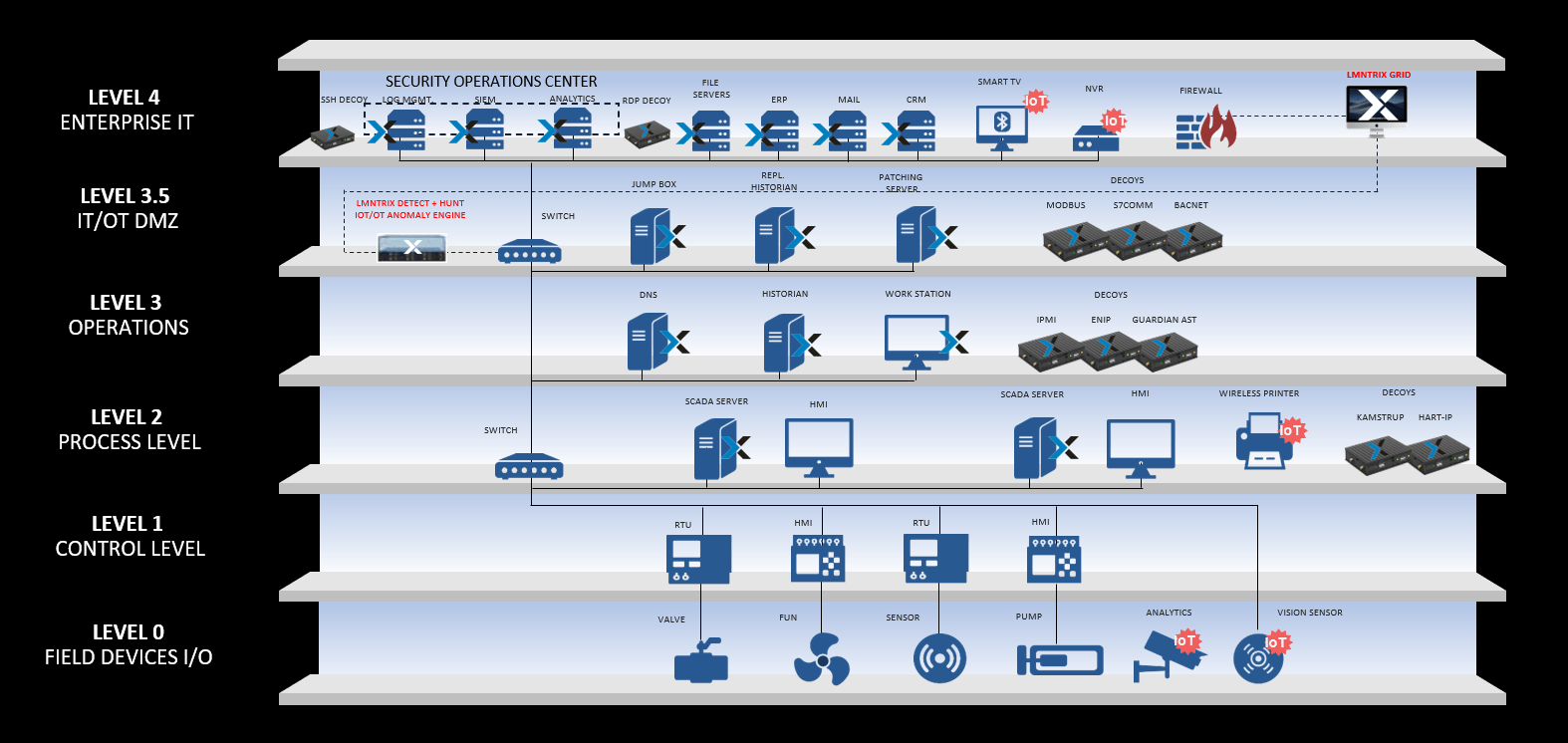
The LMNTRIX multi-vector and holistic architecture detects any threat to the SCADA application, process or network, providing granular visibility of SCADA traffic and facilitating attack forensics:
- We monitor and record all SCADA activity out-of-band and independent of the ability of SCADA devices to send logs
- We baseline normal behavior and alert on deviations from the baseline to prevent undesired network operations based upon policy
- With our integrated network and endpoint threat forensics together with deceptions everywhere we reveal the entire sequence of an attack event
- All security and events related to our architecture are centrally managed, providing a complete view across your enterprise and control networks
- We support the industry’s most extensive support of ICS/SCADA-specific protocols including BACNet, DNP3, IEC-60870-5-104, IEC 60870-6 (ICCP), IEC 61850, MMS, Modbus, OPC, Profinet, S7 (Siemens) and many others
- We detect and prevent exploits of ICS vulnerabilities with SCADA IDS signatures and on the endpoint using exploit prevention using hardware assisted control flow integrity (HA-CFI), closing the window of exposure between vulnerable and patched systems.
- We detect lateral movement using SCADA specific deceptions
- We recommend our software component (agent) installed on all Corporate endpoints in Prevention Mode. Software component (agent) installed on all PCN endpoints (Control/HMI Servers) in Detection Mode only – Not Prevention.
- It can be installed on any device permitted that supports Windows, Linux, Mac and Solaris. Recommended but not required on Control Servers and HMIs. Not recommend on any other PCS components.
- Our network sensors can utilise a full range of threat detection capabilities including deceptions, IDS, anti-malware, and sandboxing to detect inbound threats to SCADA networks
In summary our architecture provides a complete IT-OT security solution that protects the corporate network past the perimeter, the bridge between IT and OT networks and operator workstations and SCADA devices within the OT network.


