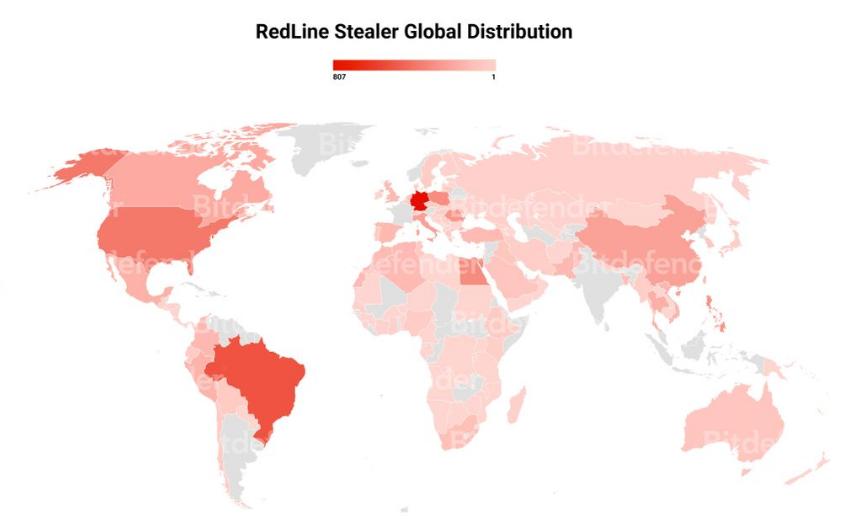
Redline Stealer is a highly effective form of malware that is designed to steal sensitive information from infected systems. It was first discovered in 2018 that it can cause significant harm to infected systems and compromise the sensitive information from victims, as elaborated herein. Redline malware is an evolving piece of malware code written in C# with notable growth in 2021 and disseminated using templates related to the COVID-19 pandemic.
RedLine Infostealer is delivered through stolen games and cracked apps. The malware steals data from browsers, Bitcoin wallets, FileZilla, Discord, Steam, Telegram, and VPN clients. The Redline infostealer sample collects information about the infected PC, including running processes, antivirus products, installed software, Windows product name, CPU architecture, etc. The redline stealer supports Download, RunPE, DownloadAndEx, OpenLink, and CMD. SOAP messages are used to transfer data that was previously exfiltrated from the target system.
Target – MS Windows Platform
RedLine Infection Vector
Redline Infostealer being versatile tends to offer many delivery methods. It has been observed by LMNTRIX CDC, that Redline has been utilised in several smaller campaigns by known and emerging threat actors. Thus, several infection vectors exist for redline infostealer.
Given below are a few of the infection vectors frequently preferred by threat actors;
- Trojanized Telegram, Signal, Discord installations.
- Email phishing campaigns with YouTube fake strike notice.
- Abusing Google Ads with Trojanized or fraudulent websites.
- Digital artists and creators have been victims of social engineering using NFT
(Non-fungible tokens)
- Malware downloader that results in drive by infection.
Infection Chain
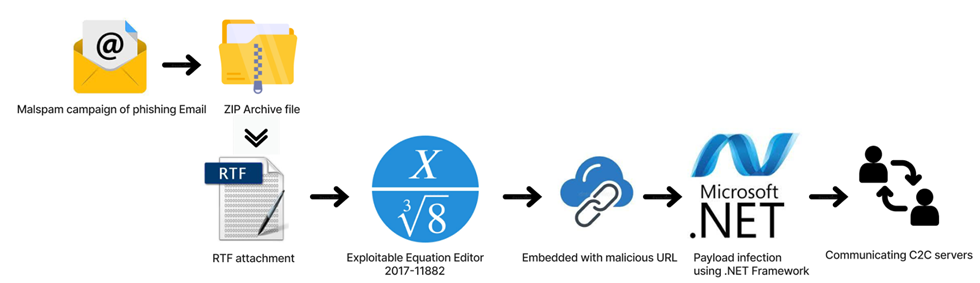
Usually the content of the email body states, “Review the order confirmation for the recent purchase, and please open the attachment file to confirm the order is complete”. So in this email, a subtle trick is used by the threat actor to urge the victim to open the attachment. Once the user opens the malspam email, they perform various malicious activities using the Office documents, try to convince the victim to disable security protections (Ex: Enable ActiveX or Macros), and so on.
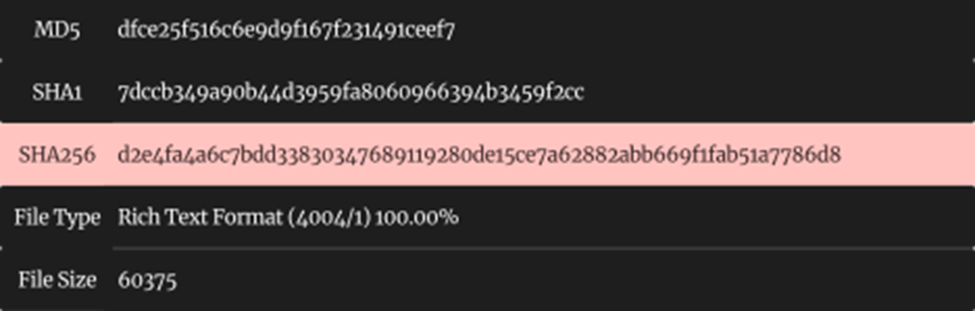
Sample Information
Threat Name: RedLine Infostealer | Classification: Infostealer | Exploit: CVE-2017-11882
Technical Analysis of RedLine RTF Malware
Rich Text Format (.RTF) is a cross-platform sharing document, and it’s intended as a universal format that could be used by most word processors, making it easier for people to share Word documents with people who don’t use Word. Also, it’s incorporated as the default format used by Windows’ built-in WordPad app, a lightweight word processor. Earlier, it was also used as the basis for the Windows help files.
In general, a normal text file stores only plain text, while RTF files can include extra information about font style, formatting, images, and more.
Main Content
After opening the attachment document, the embedded exploitable equation editor tries to exploit the victim’s system by downloading the .NET based MSIL malware to perform malicious actions.
What is the Equation Editor?
The Equation Editor is a component of Microsoft Office, used to create complex mathematical formulas and insert them into your documents, it has an executable file named eqnedt32.exe. The vulnerability enables an attacker to execute code remotely when a victim opens an affected RTF document in Microsoft Word.
CVE-2017-11882 is one of the lesser-known memory corruption vulnerabilities in Microsoft Office’s Equation Editor that enables remote code execution on vulnerable devices. Hackers might exploit the flaw by tricking users into opening specially crafted files.
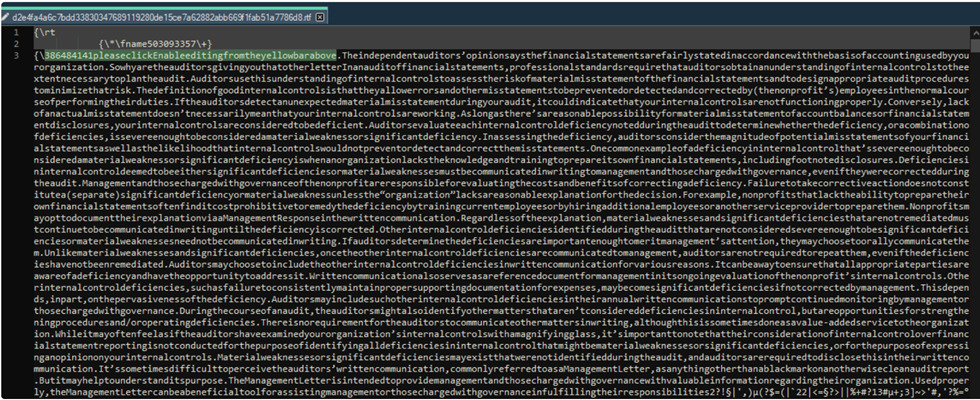
Embedded Equation Editor Functions
After extracting the object, we can skip OLE, CompObj and ObjInfo streams, and it will go directly to Equation Native stream.
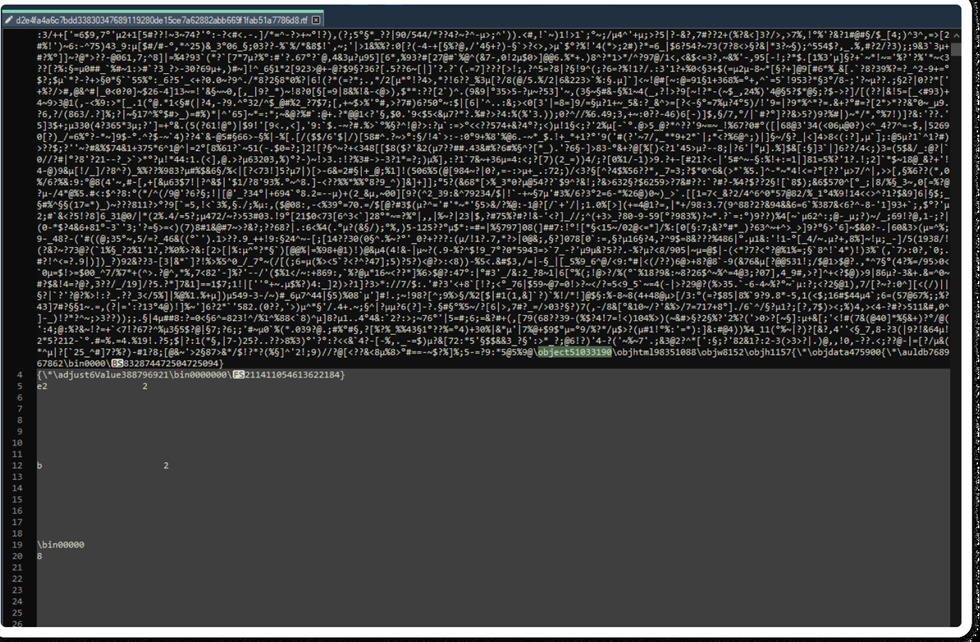
CVE Exploit Vulnerability graph over a decade
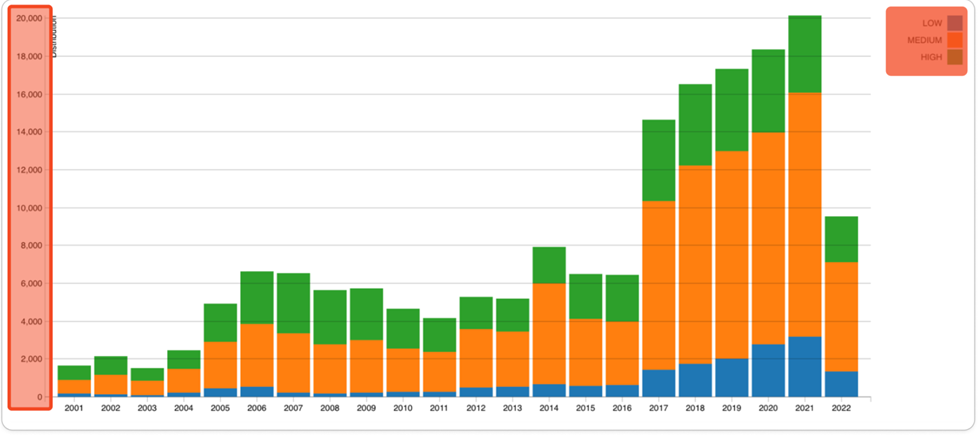
Indicator of Compromise:
In the VT results, it shows the submitted URL is malicious and it’s downloading the Redline .NET framework executable malware with embedded Base64 Encoding technique.
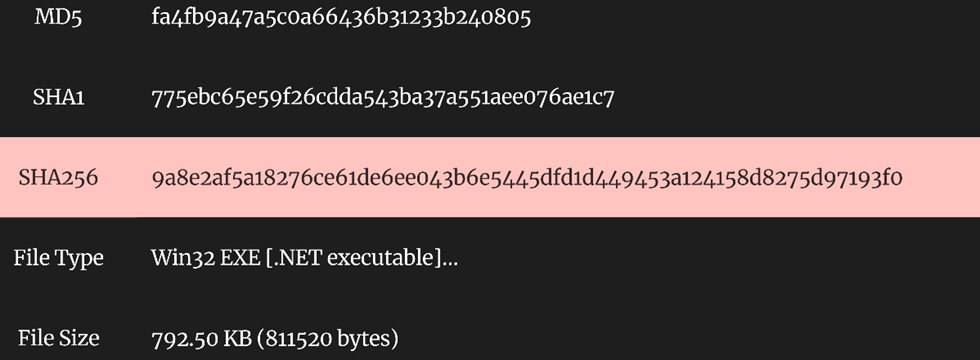
Sample Information of Dropped Payload .NET file
MSIL extensions are known as Microsoft Intermediate Language files. The code is actually compiled when the program is being executed using a just-in-time compiler, or JIT. By encrypting malicious payloads and hiding them within archive files, it provides attackers with a way of bypassing many security protections, MSIL as assembly, just on a higher level.
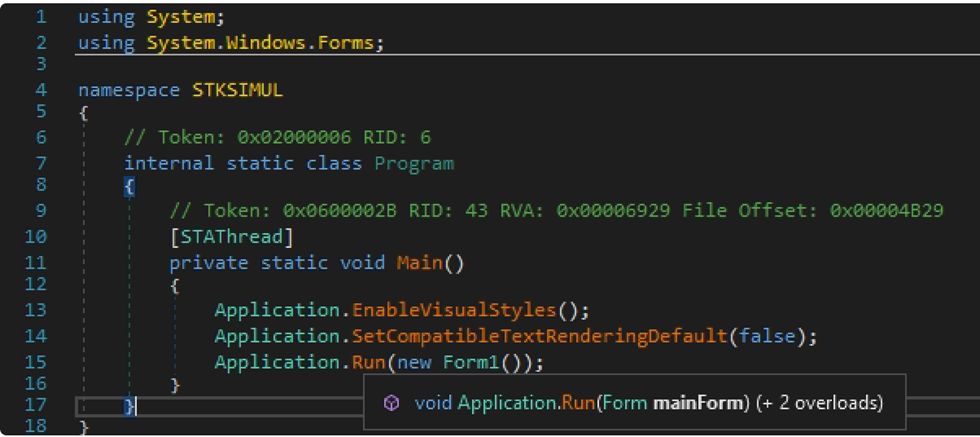
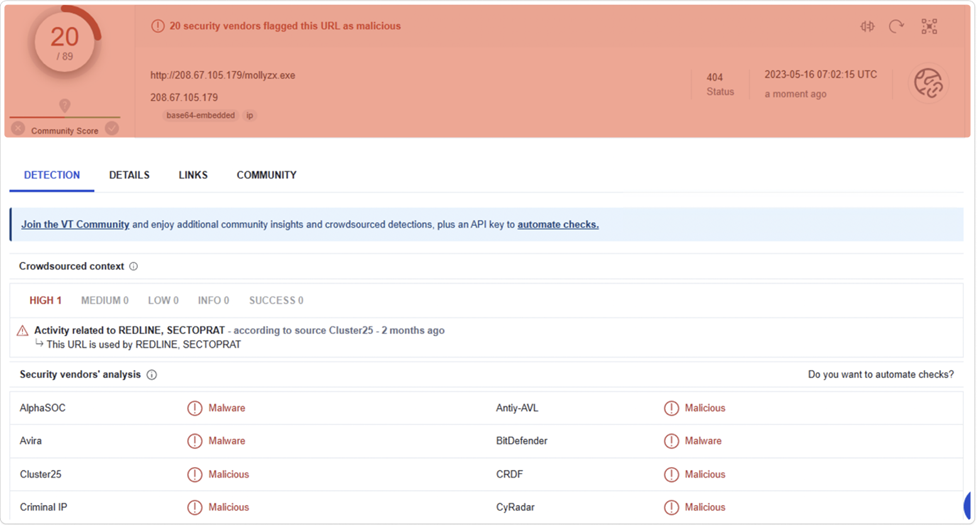
Main Entry Point of the [kox.exe]
Obfuscated INI-Component
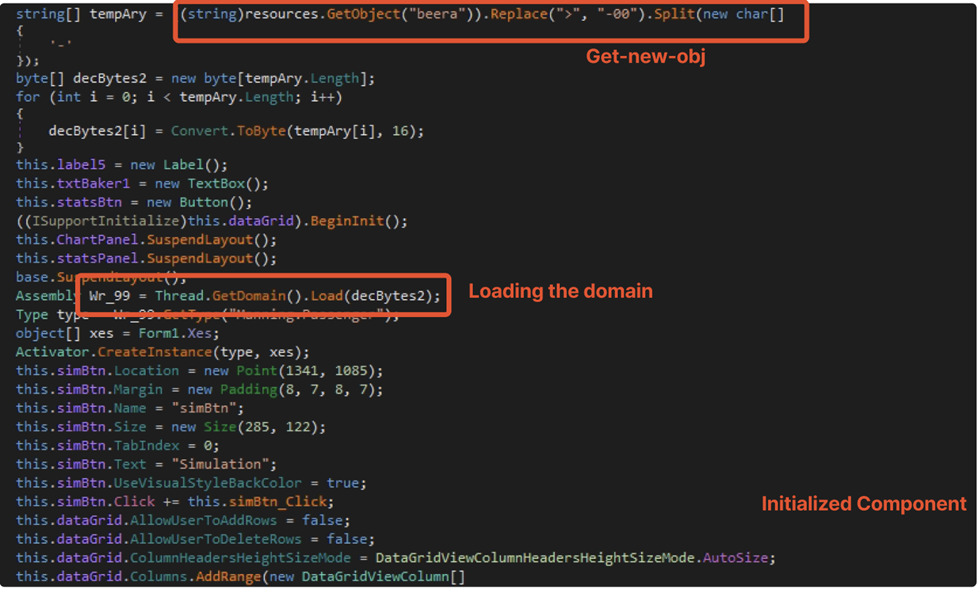
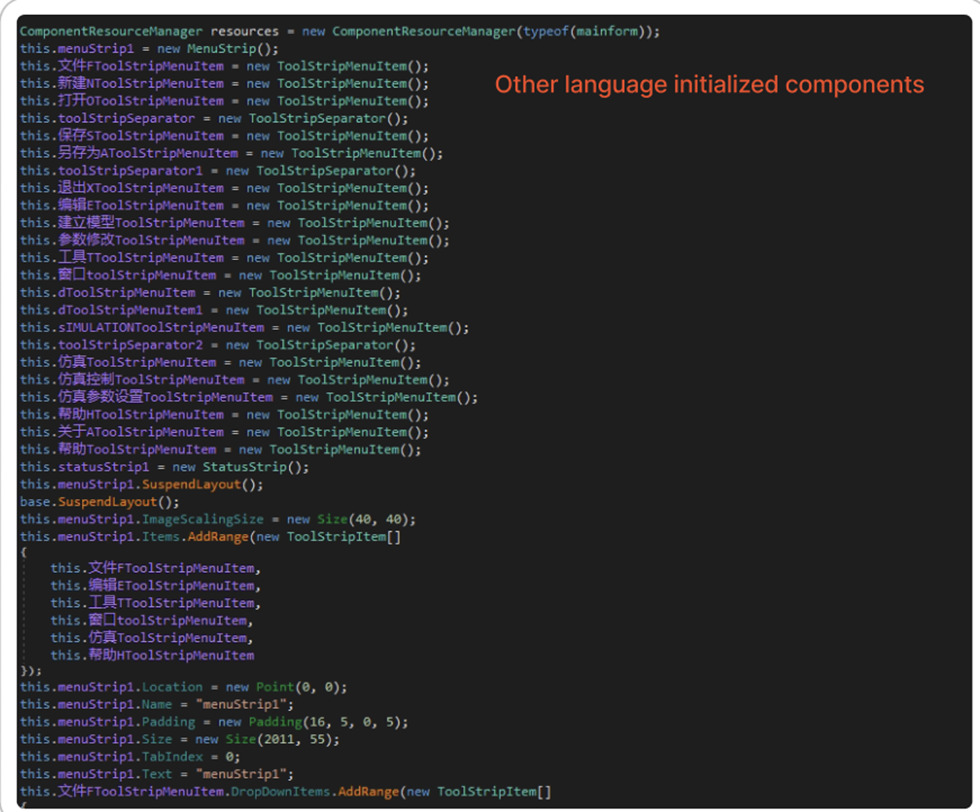
Run – Main Form1 [Initialized Component]
Like a modern supply chain, infostealer malware attacks are assisted by multiple specialized threat actors across dark web markets, forums and/or telegram channels. Not all stealer malware attacks follow the “standard” lifecycle described below. A hacktivist or threat actor might purchase a given infostealer malware, distribute it against a target by themselves, and then escalate privileges after initial access has been established on the target network.
A typical infostealer attack usually follows this lifecycle;
1) Malware as a Service vendors sell infostealer malware and C2 infrastructure on dark web forums or telegram channels.
2) Threat actor buys malware and creates the Malware as a Service distribution infrastructure.
3) Infostealer malware goes ahead and infects victims’ systems.
4) Critical data is exfiltrated to the C2 infrastructure.
5) Threat actor/group sells data on dark web forums or telegram channels.
– Cryptocurrencies like Bitcoin are used for payment.
6) Initial access brokers sell business data and logs to more threat actors.
7) Threat actors auction critical corporate data and logs to the highest bidder on dark web forums.
8) A new threat actor buys similar credentials and leverages the data for identity theft, financial fraud, account takeover, phishing scams, and ransomware attacks.
Redline Activity in the wild, as observed by LMNTRIX;
1. Stealing sensitive information: Primarily designed to steal sensitive information from an infected system, including login credentials, credit card numbers, and other personal data.
2. Keylogging: Record keystrokes from an infected system, allowing cyber criminals to capture sensitive information entered by the victim.
3. Capturing screenshots: Capture screenshots of the victim’s system, allowing attackers to monitor the victim’s activity and steal sensitive information.
4. Spreading & Lateral Movement: Spread to other systems on the same network or via removable media, such as USB drives, allowing it to infect additional systems and perpetually propagate Redline’s malicious activities.
Interesting file names from the Redline sample;
{{
payment.doc
kox.exe
mollyzx.exe
mollybt41862.exe
775ebc65e59f26cdda543ba37a551aee076ae1c7.bin
}}
Indicators of Compromise for Redline Infostealer
Hashes:
- 6cc44d98ce2fb628b25519eb2aa476b81c1dca23b4c11fb3f26951bba8e68d64
- 5be845902145831466d3b710541d2c5a53cfc50108126c8802b48226e89e1887
- 1365e7708c818aa8a3cbed2a295ce2d585c654d80b78b1e5b3af9f30c654a4fa
- 7701ee20f7c99aadf95e31bf775bf1614f66aea3e9f03dfadf5ee247ab8eb29c
- 1d18b3c7e5845a5c5cf519471a7b6ee354f848764b7c64b6f3ec59d0e3492e9b
- 710b3f75954a006368d8ebff83e35a8c815f26bdf2b58d62e1a5ffdbc88cd20f
SHA 1 Hashes:
- 61F9DBE256052D6315361119C7B7330880899D4C
- ADCE7CA8C1860E513FB70BCC384237DAE4BC9D26
- F6F1C1AB9743E267AC5E998336AF917632D2F8ED
- 6C404F19EC17609AD3AB375B613EA429E802F063
IP:
- 95.179.163[.]157
- 193.106.191[.]226
- 49.12.69[.]202
- 185.250.148[.]76
- 172.245.45[.]213
Domains:
- tempuri[.]org/Entity/Id<1-24>
- santaanarealtor[.]icu
MITRE ATT&CK Tactics & Techniques for Redline Infostealer
| ID | Tactic | Technique |
| TA0001 | Initial Access | Spear Phishing Attachment Phishing URL |
| TA0002 | Execution | Exploitation for Client Execution |
| TA0003 | Persistence | Path Interception Boot or Logon Initialization Scripts Logon Scripts |
| TA0004 | Privilege Escalation | Process Injection Logon Scripts (Windows) |
| TA0005 TA0006 | Defense Evasion Credential Access | Disable or Modify Tools Obfuscated Files or Information Registry Modification Virtualization/ Sandbox Evasion OS Credential Dumping LSASS Memory Security Account Manager NTDS LSA Secrets |
| TA0007 TA0008 TA0009 | Discovery Lateral Movement Collection | Security Software Discovery System Network Configuration Discovery Process Discovery File and Directory Discovery & Query Registry Remote Desktop Protocol SMB/ Windows Admin Shares Archive Collected Data Data from Local System |
| TA0011 | C&C Server | Data Obfuscation Ingress Tool Transfer Web Protocols – Standard Application Layer Protocol. |